[the security toolkit for fast-paced modern development and deployment]
.png&w=3840&q=75)
Protection
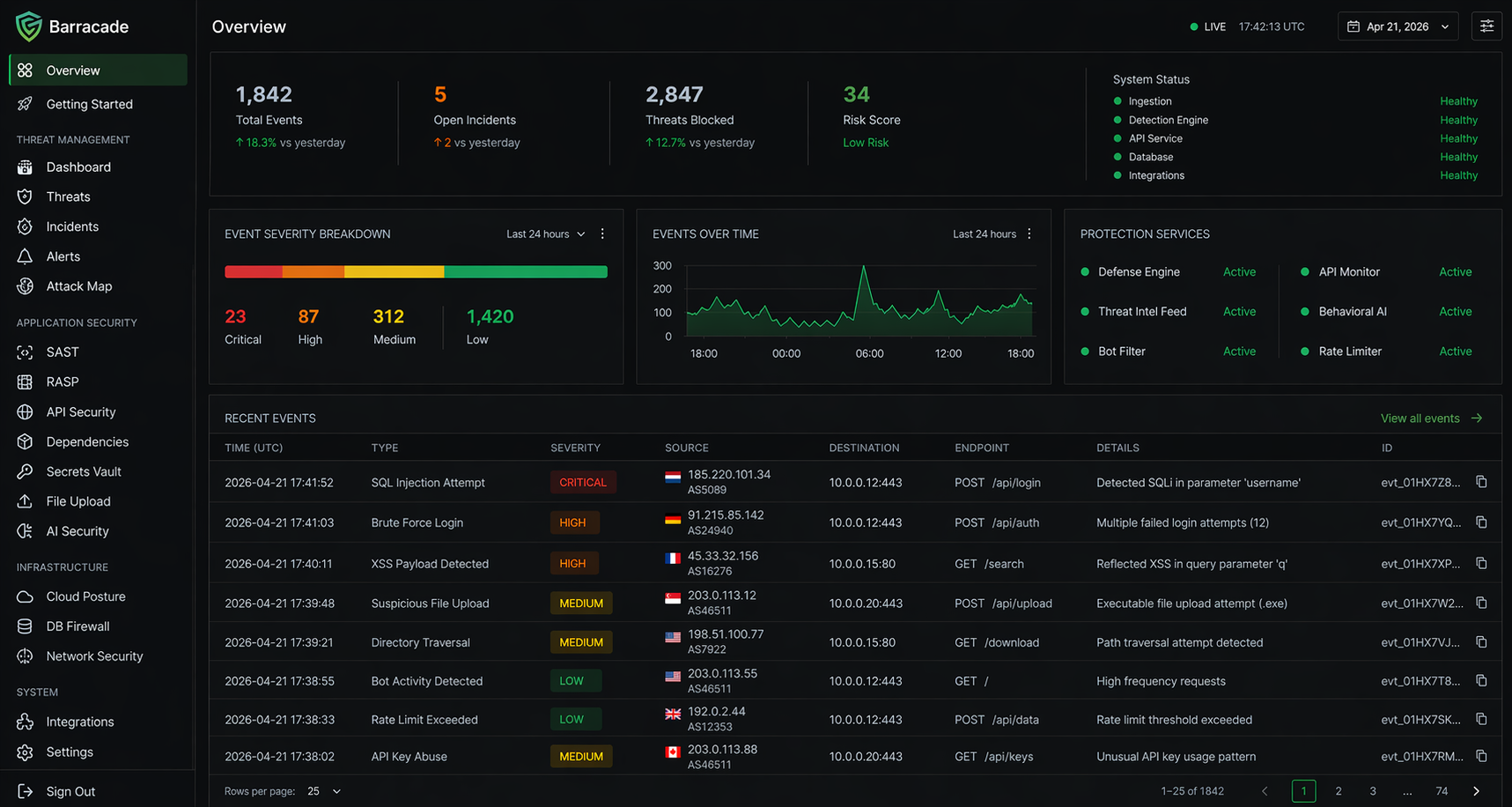
RASP engine with 15 real-time detectors covering SQL injection, XSS, SSRF, command injection, path traversal, and 10 more attack types. Three modes: monitor, block, or learn.
Analysis
Static analysis across 8 languages covering 23 vulnerability categories. Generates a code patch for every finding so you can fix issues without having to research each one.
Compliance
Maps findings to 9 frameworks: SOC 2, ISO 27001, GDPR, HIPAA, PCI-DSS, NIST 800-53, CIS, CCPA, and FedRAMP. Automated evidence collection and gap analysis.
Discovery
Attack surface mapping across subdomains, DNS records, and exposed services, credential breach monitoring, pipeline and container scanning, and website security audits with letter grades.
Works with your stack.
Barracade connects to the tools you already use. Push to GitHub and the scan runs. Deploy to Vercel and the pre-deploy check runs. Get a Slack message when something needs your attention.
Scans repos on every push and blocks secrets from reaching your commit history.
Surfaces SAST findings and dependency alerts inline as AI generates new code.
Extension shows vulnerability warnings and patch suggestions without leaving your editor.
Runs a pre-deploy security check on every build. Fails the deploy if critical issues are found.
Monitors exposed credentials, weak RLS policies, and anomalous query patterns in real time.
Audits containers for misconfigurations and scans environment variables for exposed secrets.
Sends a message to your channel the moment a credential surfaces in breach data or an attack fires.
Opens an issue for every finding automatically, with severity, affected file, and a generated patch.
Built for what comes next
AI tooling generates code that ships without a security review. Barracade sits alongside your application, detecting vulnerabilities before deployment, intercepting attacks at runtime, and alerting you when credentials or infrastructure get exposed.
Fourteen modules operating as one system. When static analysis flags a hardcoded secret, breach monitoring registers it automatically. When RASP intercepts a runtime attack, the defense engine enforces your configured response policy. Every module feeds the others.
Not a report you run once. Barracade runs continuously alongside your deployed software, monitoring domains, watching breach databases, enforcing RASP policies, and alerting on regressions as long as your application is live.
Security for the
AI-coding era
AI tooling ships code without a security review by default. Barracade is the active protection layer: intercepting attacks mid-execution via RASP, hardening your codebase before deployment, and continuously monitoring everything you've released.
Real results.
Security stops being something you get to eventually. Barracade runs alongside what you are already doing, so checks happen on every build, patches are generated for every finding, and exposure monitoring runs in the background continuously. The workflow change is small. The coverage difference is not.
Active protection for AI-built software.
AI development tools are built to optimize for speed. Security review doesn't fit that workflow, so it gets skipped, not out of negligence but because no capable tool has been built for that reality. Barracade is that tool. It runs alongside your application, actively detecting threats, enforcing security policies, and protecting what you've built as it runs in production.
Detects and intercepts attacks in real time
RASP instruments your application from within the process. SQL injection, XSS, SSRF, command injection, and 11 more attack vectors are intercepted mid-execution before they reach your application logic. No proxy, no WAF, no network reconfiguration required.
Hardens your codebase before it ships
Static analysis, dependency scanning, secrets detection, pipeline hardening, and container auditing run against your code and infrastructure before deployment. Findings come with generated patches, not reports to research.
Continuously monitors what you've deployed
Attack surface monitoring, credential breach detection, and site health tracking run in the background against your live infrastructure. Barracade alerts you when your external footprint changes, credentials surface in breach data, or a deploy introduces a regression.
15
attack vectors intercepted by RASP in real time, no proxy required
14
modules sharing findings as one unified security system
9
compliance frameworks mapped continuously, from SOC 2 to HIPAA
Static analysis
Scans source code for 23 vulnerability categories across JS, TS, Python, Go, Rust, Java, C#, and PHP. Reports include file, line, severity, description, and a generated code patch. Scan scope is configurable: single file, directory, repository, commit, or PR. Exports as SARIF.
Every finding includes a generated diff for that exact block of code. Review it, apply it, or edit it before anything changes on disk.
Dependency scanning
Reads lock files from 12 package ecosystems, builds a full dependency tree, and cross-references against the NVD. Scores each finding with EPSS exploit probability. Also catches typosquat packages, license violations, and generates CycloneDX 1.5 or SPDX SBOMs.

Runtime protection
RASP instruments your application from within the process. Malicious requests are intercepted and logged before they reach your code. No proxy, no WAF rules, no network reconfiguration required.
15 Attack vectors
Catches query manipulation in parameters, headers, and bodies
Reflected and stored XSS across any input surface
Stops internal network probing via user-supplied URLs
Prevents shell execution through app inputs
Blocks directory escape in file path parameters
__proto__ and constructor manipulation in JSON payloads
XXE detection in XML parsers and SOAP endpoints
Catches unsafe deserialization in JSON, YAML, and binary formats
Detects CL/TE and TE/CL mismatches in HTTP pipelines
CRLF injection and response splitting
Filter manipulation in directory service queries
Operator injection in MongoDB and similar databases
Catches catastrophic backtracking in user-supplied patterns
Validates redirect targets against your allowed domains
Prevents unintended exposure of file system contents
Attack surface discovery
Enter a domain and Barracade maps every subdomain, exposed service, and DNS record in your external footprint. Subdomains are found through certificate transparency logs and DNS enumeration, including assets you deployed months ago and forgot about.
Dangling CNAME entries that could be taken over get flagged immediately. Scheduled re-scans run in the background and alert you when new assets appear or an existing one drops in security grade.
example.com / scan results
More modules
Pipeline security
Scans GitHub Actions workflows, Dockerfiles, and CI configs for exposed secrets, unpinned third-party actions, and permissions that are broader than they need to be.
Container and IaC
Dockerfiles, Kubernetes manifests, Terraform, and CloudFormation scanned for root containers, public S3 buckets, wildcard IAM policies, and unencrypted storage.
Breach monitoring
Watches breach databases and public code repositories for your API keys, tokens, and domain credentials. Alerts you when something shows up where it should not be.

Compliance mapping
Takes your scan results, RASP config, and code findings and maps them to 9 compliance frameworks: SOC 2, ISO 27001, GDPR, HIPAA, PCI-DSS, NIST 800-53, CIS, CCPA, and FedRAMP. Cross-framework control mapping means a single fix can close gaps across multiple standards.
Coverage updates automatically as findings are resolved. Export as PDF for auditors or integrate with GRC tooling.
Website scanning
Enter a URL and Barracade audits TLS configuration, response headers, cookie flags, exposed endpoints, and CMS-specific issues. Results include a letter grade and a prioritized remediation list. Most scans complete in under 10 seconds. Batch scanning across multiple domains is supported.
Security headers
Select the headers you need, choose your deployment platform, and generate copy-ready configuration for your project.
Headers: CSP, HSTS, X-Frame-Options, X-Content-Type-Options, Referrer-Policy, Permissions-Policy, CORP, COEP, COOP.
Platforms: Next.js, Vercel, Netlify, Express, Nginx, Apache, Caddy, Cloudflare Workers.
Site health monitoring
Register your domains and Barracade tracks their security grades over time. Scheduled re-scans detect regressions automatically, like a deploy that drops HSTS or exposes server version headers.
Grade history is tracked per domain. Review trends across days, weeks, or months.
Secrets vault
Stores API keys, database credentials, OAuth tokens, and SSH keys encrypted with AES-256-GCM. Organized by project with expiry tracking and rotation alerts.
When the static analyzer detects a hardcoded secret, Barracade can migrate it to the vault and replace it with an environment variable reference. Export as .env for deployment.